Security and Privacy are key in todays digital first world. Setting up a VPN with OpenVPN in Microsoft Azure offers a fairly simple method to add an additional option to increase your security and privacy online. This is true for both personal and enterprise purposes. Using a VPN, will allow you to stay secure regardless of what Wifi hotspot or network you’re connecting to the Internet through.
Sure, there are many different VPN services you can use, and many are fairly cheap themselves. However, how do you know you can really trust them? With setting up an OpenVPN server in Azure, you will be able to know you can trust the VPN server for your own use. Also, you will know that only you will be able to access the VPN and the data that may be stored on the server. This will help not just add more security and privacy to your Internet usage from anywhere, but it’ll also add to your peace of mind overall.
Table of Contents
What is OpenVPN?
OpenVPN is a VPN (Virtual Private Network) solution that helps you secure your data communications. There are other VPN solutions available, but OpenVPN provides an easy to use interface for configuration of the Access Server, in addition to an easy to use OpenVPN Connect client application to get your devices connected.
OpenVPN can easily be installed on any server or virtual machine (VM) to provide a more secure and private Internet experience for you and your users. Setting up OpenVPN can be beneficial to many different usage scenarios, including:
- Increased Internet privacy from your local ISP or Wifi hotspot
- Provide more secure remote access for employees
- Secure IoT solutions
- More secure cloud and hybrid networking scenarios
Setup OpenVPN in Azure
Setting up an OpenVPN server in Microsoft Azure is made easier with the help of the OpenVPN Access Server image made available in the Azure Marketplace by OpenVPN Inc. Provisioning a VM using this image will automatically have OpenVPN installed, and all you need to do is configure it for your needs.
Let’s take a look at the steps necessary to create a new OpenVPN server virtual machine in Azure, and configuring it for use!
Create a OpenVPN Virtual Machine in Azure
- Open the Azure Portal, and search the marketplace for OpenVPN then select the OpenVPN Access Server option.

- On the OpenVPN Access Server, select the Start with a pre-set configuration button to get started with provisioning.

- On the Choose recommended defaults that match your workload step, you’ll want to choose an option that reflects what you are looking to do with the VPN server. If you are looking to just setup a simple VPN server for Personal or Dev/Test use then select the Dev/Test workload environment option and the General purpose workload type for now. You will configure the actual Virtual Machine size / pricing tier in a future step so don’t worry about that right now. Then select the Continue to create VM button.

- On the Create a virtual machine step, start by specifying the Resource group and Virtual machine name for this VM on the Basics step.

- Next, choose the geographic location you wish to host the VPN server within by setting the Region field. This will specify the Azure Region where the VM will be running, and thus what part of the world it will get its Internet access from. Depending on your intended use for the VPN, you may want to use an Azure Region near you, or one located in a different country or part of the world.

- Next, choose the Size of the VM. This sets the pricing tier and will determine how much your OpenVPN server will cost to run. The cheapest option is the Standard_B1s size with 1 vcpu and 1GiB memory. Selecting this VM size should be sufficient for at least one or two clients connected to the VPN. To conserve cost, I recommend starting small here (especially if you’re setting this up for personal use), then you can always resize the VM to give it more compute resources later if necessary.

- Next, set the Administrator account credentials. This is the credentials that the VM will be configured with for the Administrator account you will use to connect to the VM over SSH to configure it. For greater security, it is recommended that you use SSH public key, but for simpler setup you can alternatively choose Password and specify your own username and password to use.

- Select the Review + create button to move forward with creating the VM. You can leave the other configuration tabs to their default values, unless you know what more advanced configurations you wish to set.
- Once the validation has passed, go ahead and select the Create button to start the provisioning processes of creating the new OpenVPN Virtual Machine as you’ve configured.
Configure OpenVPN over SSH
Once you have an OpenVPN VM provisioned in your Azure Subscription, you will need to setup OpenVPN on it. This step is really simple to do thanks to the Azure Marketplace virtual machine image you chose to create the OpenVPN server with, and thanks to the OpenVPN team for providing it.
From within the Azure Portal, follow these steps to get OpenVPN configured:
- Navigate to your OpenVPN virtual machine, and copy the Public IP Address for it.

- Next, we will connect to the VM to configure it using SSH. This can be done using the Azure Cloud Shell directly from the Azure Portal. To open the Azure Cloud Shell, click the Cloud Shell icon in the right side of the top menu bar of the Azure Portal.

- Within the Azure Cloud Shell, run the
sshcommand to connect to the VM.
Run the followingsshcommand by filling in your Administrator account username that was configured for the VM, and the IP Address that was just copied.ssh <username>@<ip-address> - When prompted to continue connecting, confirm by typing
yesand hittingEnter. This prompt is due to a self signed certificate being used to encrypt the SSH connection, and is expected since this hasn’t been configured otherwise. Also, you don’t need to be concerned with this as this is the only time you will be connecting to the VM over SSH. Once configured you wont need to connect over SSH again.
- When prompted, enter the
Passwordthat was configured for theAdministrator Account. - Next, you will be prompted with different configuration options for setting up OpenVPN.
- On the prompt to accept the agreement, type
yesPlease enter 'yes' to indicate your agreement [no]: _ - On the Primary Access Server node prompt, type
yesto since this is the only node you’re creating.Will this be the primary Access Server node? - When prompted with what network interface and IP address to choose for the Admin Web UI, choose the
1option forall interfaces: 0.0.0.0.
- When prompted for the port number to use for the Admin Web UI, select the default of
943.Please specify the port number for the Admin Web UI. - When prompted for the TCP port number to use for the OpenVPN Daemon, select the default of
443.Please specify the TCP port number for the OpenVPN Daemon - When prompted if all client traffic should be routed by default through the VPN, type
yes. This will ensure that all Internet traffic from your device(s) will be sent through the VPN when connected.Should client traffic be routed by default through the VPN? - When prompted if all DNS traffic should be routed by default through the VPN, type
yes. This will ensure that all domain name resolution (DNS) from your client(s) will be sent through the VPN when connected.Should client DNS traffic be routed by default through the VPN? - When prompted if an internal DB should be used for local authentication, type
yes. This will configure OpenVPN to use its own access list of usernames / passwords for user of the VPN.Use local authentication via internal DB? - When prompted if private subnets should be accessible to clients, hit
Enterand accept the default ofyes. This only matters if you have other resources in Azure connected to the same Virtual Network as the OpenVPN VM.Should private subnets be accessible to clients by default? - When prompted if you wish to login to the Admin UI as “openvpn”, decide if this is the admin username you want to use for configuring OpenVPN. Be default the admin username will be “openvpn”, but it’s recommended you change enter
noand configure your own admin username. A different username than the default will make it more difficult for you OpenVPN server to get hacked.
- When prompted to specify your Activation key, please it blank and hit
Enter. - Now, OpenVPN is finishing configuration. This will take a few seconds to complete.
- You will see an Initial Configuration Complete! message once setup is complete. The terminal output will now list the Admin Web UI and Client Web UI URLs for your OpenVPN server. You can use the Admin Web UI

- Save the information displayed in the terminal for your future reference. Also, make sure you save the usernames and passwords entered.
Now that you have the OpenVPN server setup and configured, you can use the OpenVPN Connect app on your device to connect to and use the VPN. Initially, you can use the username and password configured for the “Admin UI” to use the VPN. However, you can also use it to login to the “Admin Web UI” URL and configure the OpenVPN server and add additional user accounts as necessary.
Tip: By default, IP Addresses for Virtual Machines in Azure are dynamically assigned. This means that if the VM gets deallocated for some reason, your OpenVPN IP Address might change. This can happen if you resize the VM, or if Azure has an internal reason to move your VM within the datacenter. As a result, it’s a good practice to setup the DNS name for your OpenVPN virtual machine in Azure, so you can use a Domain Name to connect clients to the VPN; instead of the IP Address directly. Alternatively, you could also setup a custom domain mapping if you want a more advanced setup.
OpenVPN Access Server Licensing
The OpenVPN Access Server is free to use for up to 2 simultaneous VPN connections to any single OpenVPN server. If you require more simultaneous connections to your VPN server, then you will be required to purchase a license from OpenVPN. The OpenVPN image from the Azure Marketplace is a BYOL (Bring Your Own License) image, so your OpenVPN server will be free to use with this 2 simultaneous connection limit, unless you register a purchased license with your VPN server.
OpenVPN Free License: The OpenVPN Access Server is free to use for up to 2 simultaneous VPN connections.
The 2 simultaneous license limit will work great for a number of different usage scenarios where you only require a small number of clients to connect. This can fit certain enterprise scenarios, but you’ll want to make sure to double check the OpenVPN Access Server licensing for further details. When it comes to personal use, however, you may find that the 2 simultaneous connection limit will still work great. Plus, you can always setup multiple OpenVPN virtual machines in Azure to accommodate additional connected devices, if this is something that works for your scenario.
The OpenVPN website contains additional information about OpenVPN Access Server licensing, including the Bring Your Own License (BYOL) pricing that you’ll use with the Azure Marketplace image for OpenVPN.
Tips to Save Money
The cost of the OpenVPN server in Azure will largely depend on the VM size you chose to host the VM with. In addition to this, the VM disk storage will have a small cost associated with it. However, with a VPN server, the bulk of the overall cost will be dependent on how much bandwidth you use when connected.
Here are a couple of additional tips you could use to help reduce the overall cost of your new OpenVPN server:
- Stop when not in use: When not in use, go into Azure and Stop the VM so it’s placed in a Stopped (deallocated) state. This will stop the VM so you don’t have to pay for running it when not needed. Although, you will need to Start the VM again before the next use. If you only use the VPN when traveling, this could really help conserve cost when you’re not out of town.
- Disconnect when not needed: Since bandwidth usage of your VPN will cost money in Microsoft Azure, you can simply disconnect your computes / devices when from the VPN when you don’t really need them connected. Also, streaming video (such as YouTube, Netflix, and others) can consume a lot of bandwidth, so you may want to avoid using these services while connected to the VPN.
- Resize the VM Instance Size: The compute cost of running a VM in Azure depends on the VM Instance Size / pricing tier you choose for the VM. This can be resized at any time, and you can use this to manually change to a lower cost pricing tier that still works for your needs. Just keep in mind that changing the VM Size will reboot the VM, so you’ll want to factor this into the affect it will have on any connected clients.
Connect to VPN with OpenVPN Connection
When connecting devices to a VPN hosted with OpenVPN, you will need to use the OpenVPN Connect client application. There is a distribution of this application for all operating systems. On mobile platforms (iOS and Android) you can download this from the App Store.
Also, if you need help locating the client, you can login to the OpenVPN Web UI, where you will see links to download the OpenVPN Connect client application for your device(s).

Once the OpenVPN Connect client application has been downloaded, you can configure it with your OpenVPN server and credential details for you device to connect to the VPN. Overall, the OpenVPN Connect application is really simple to use and doesn’t require a lot of technical knowledge and skill. This can help with instructing people on how to connect to and use your VPN.
Here’s a loot at connecting an Apple iOS device to the OpenVPN:
- Download the OpenVPN Connect application from the App Store.

- Select to Import a Profile, and enter in your OpenVPN server information. This would be the IP Address (or DNS name) of the OpenVPN server, and the Username / Password to connect with.

- When prompted, select to Allow the OpenVPN app to add VPN configurations to your device.

- When needed, open the OpenVPN app on your device and select the configured VPN you wish to connect to, or disconnect from.

- When connected to the VPN, the OpenVPN Connect app on your device will display some bandwidth usage information that you can use to help understand how much bandwidth you are using.

Wrap Up
There are a few security and privacy reasons and benefits to using a VPN. These benefits apply whether you are using it for your own personal use, or even as an enterprise that needs to secure your business and customer data. There are a lot of VPN services available for privacy and personal use, but it’s difficult to tell whether they can be trusted with your data. And, for enterprises, you likely need to use a VPN to allow your users and/or customers to securely connect to your systems. Regardless of your reasons and underlying purposes of needing to setup a VPN, the OpenVPN Access Server is fairly simple to setup get started using; while also supporting many more advanced features as well.
Hopefully, you’ll find it easier to keep your privacy and security on the Internet with the use of a VPN. And with OpenVPN it’s really simple to get setup, and add more privacy and security to your personal and/or enterprise Internet use. Yes, of course, there are more advanced VPN setups that can be done with Microsoft Azure that will likely fit an enterprise scenario much better, but it’s great to have such an easy to setup option such as OpenVPN!
Enjoy your added security and privacy online!
Original Article Source: Easy to Use VPN with OpenVPN in Azure written by Chris Pietschmann (If you're reading this somewhere other than Build5Nines.com, it was republished without permission.)


 Run Gemma 4 Locally with GitHub Copilot and VS Code
Run Gemma 4 Locally with GitHub Copilot and VS Code
 The Software Dark Factory and the Future of Software Development
The Software Dark Factory and the Future of Software Development
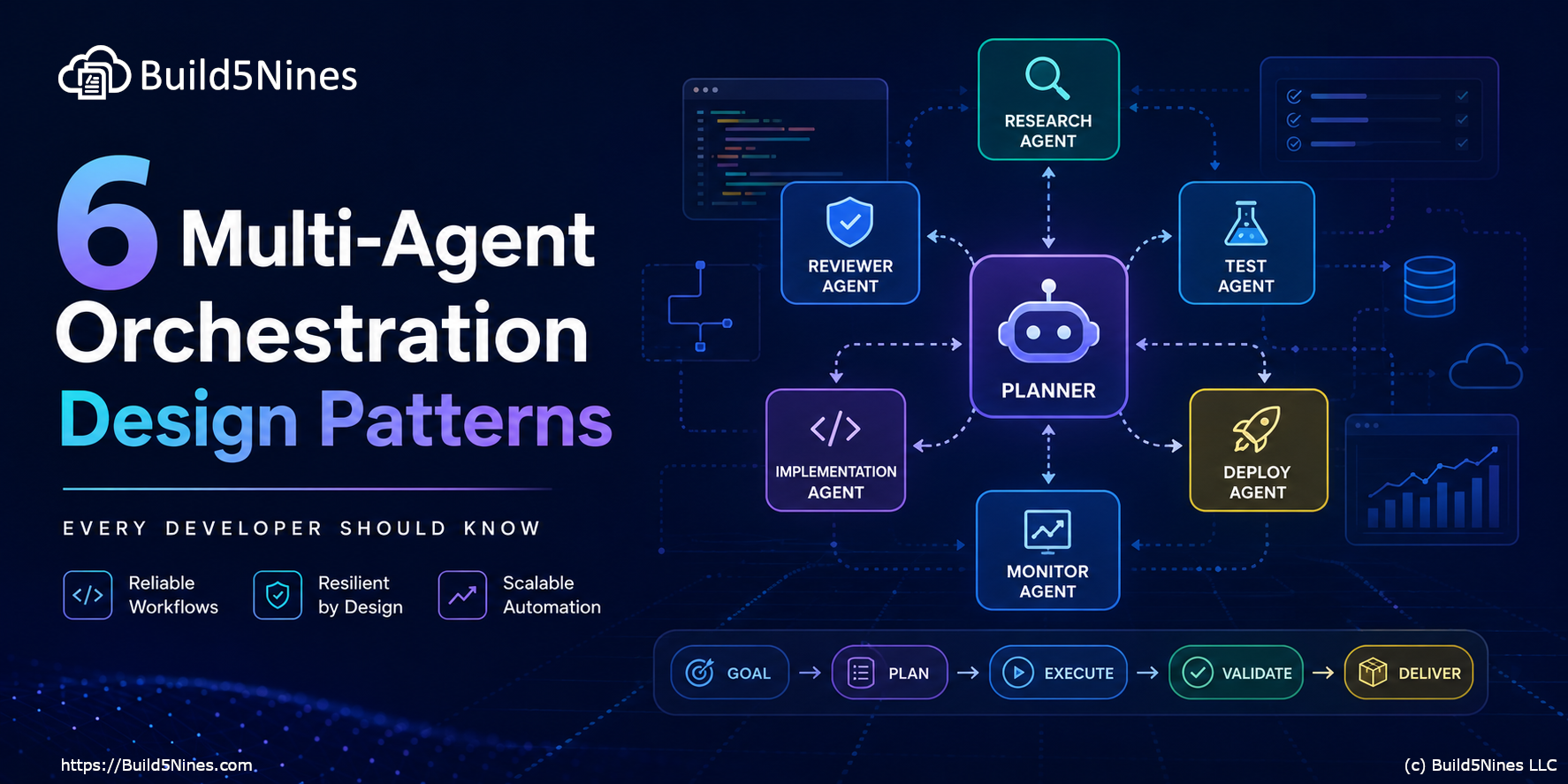 6 Multi-Agent Orchestration Design Patterns Every Developer Should Know
6 Multi-Agent Orchestration Design Patterns Every Developer Should Know
 Microsoft Azure Regions: Interactive Map of Global Datacenters
Microsoft Azure Regions: Interactive Map of Global Datacenters
 Stop Hard-Coding “Local IP” in Terraform: Lock Down Firewalls Dynamically
Stop Hard-Coding “Local IP” in Terraform: Lock Down Firewalls Dynamically