
Recently, a new Remote Desktop (RDP) and SSH remote access service in Microsoft Azure came to my attention. In short, Azure Bastion enables the Azure Portal to provide the UI for remotely and securely connecting via RDP and/or SSH to Azure Virtual Machines (VMs) within a Virtual Network (VNet). All this is without the need to add any Public IP Addresses to the VMs; thus eliminating the need to use a “Jumpbox” to access your private networks in the cloud.
What is Azure Bastion?
Azure Bastion is a resource that can be deployed to an Azure Virtual Network (VNet). Once deployed, Bastion can then be used to remotely connect to Azure Virtual Machines (VMs) within that VNet by using the Azure Portal as the client. All this is done without needing to add any public IP address to the VM. Plus, it supports both RDP and SSH connections to Azure VMs within a VNet.
Bastion enables the use of the Azure Portal to perform the Remote Desktop (RDP) connection to the VMs. This removes the requirement to use or install Microsoft Remote Desktop on your local computer. While Microsoft Remote Desktop does support both Windows and macOS, it’s simpler to connect through the Azure Portal using any web browser.
Additionally, without needing to setup any Public IP address to the Virtual Machines in the VNet, this eliminates the need for any kind of Jumpbox. If you don’t know, a Jumpbox is a single VM added to a network that can be remote into, then once connected to the Jumpbox the administrator can remotely connect to and manage any other VMs in that network.
FYI, another term for “Jumpbox” in the IT industry is a “Bastion”.
This service greatly simplifies the ability to remotely connect to and manage the VMs of an Azure cloud-bases solution. There is a cost savings by removing the need for a Jumpbox VM, as well as security benefits by removing the need to add a Public IP address to any VMs in the VNet if it’s not otherwise necessary.
Is it Secure?
Since Azure Bastion allows you to RDP or SSH through the Azure Portal UI, it’s secured using SSL/TLS encryption. Also, while removing the need for a Jumpbox, you will no longer need to setup, configure or manage any publicly facing VMs in an otherwise private, behind the firewall network.
If you look at what Azure Bastion offers, it’s probably more secure to use Bastion rather than the traditional Jumpbox method.
How to RDP to Azure VM using Azure Bastion
Here are some simple steps to remoting into an Azure VM using Azure Bastion, directly from within the Azure Portal:
- First, an Azure Bastion resource needs to be deployed in the Virtual Network (VNet)

- Navigate to the Virtual Machine (VM) that you want to RDP into. Note that this VM does not require a Public IP Address for this to work.

- Click on the Connect button to open up the pane for accessing the remote connection options for the VM.

- Azure Bastion natively integrates into the Connect pane in the Azure Portal. On the Bastion tab, simply fill in the Username and Password for the VM and click Connect.
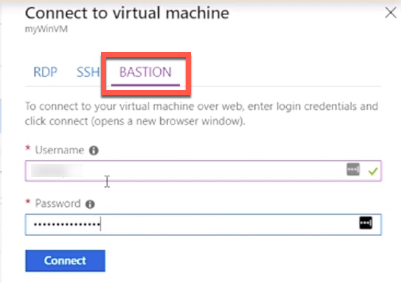
- Azure Bastion will then open the RDP connection experience directly within the Azure Portal.

Use Azure Bastion to SSH into Linux VM
Azure Bastion can also be used to remotely connect via SSH into Linux VMs in Azure as well. This works in the same fashion without the need for a Public IP Address, and directly within the Azure Portal.

More Information
There seems to be limited information about Azure Bastion, as it’s a very newly announced service for Microsoft Azure. I came across the “RDP to Azure Virtual machines using Azure Bastion” video on the official Microsoft Azure YouTube account. I watched that video, and searched Azure.com for “Bastion” and found the following additional video links:
- https://azure.microsoft.com/en-us/resources/videos/introduction-to-azure-bastion/
- https://azure.microsoft.com/en-us/resources/videos/introduction-to-bastion-ssh/
It appears that there’s not much documentation for Azure Bastion yet released. With the help of the limited documentation available at this time, and the published videos from Microsoft, I was able to write up this article on this rather interesting new service.
Conclusion
The ability to RDP or SSH to Azure VMs directly in the Azure Portal is a pretty cool feature. The fact that it doesn’t require you to add any Public IP Addresses add to its greatness, as this really enhances and changes the entire notion of a Jumpbox for accessing your Azure VMs remotely.
Attribution: Credit needs to be given to the Microsoft videos on Azure Bastion. These videos is where I was able to learn about Azure Bastion, and capture screenshots used in this article.
Original Article Source: Azure Bastion: VM RDP & SSH Access within Azure Portal written by Chris Pietschmann (If you're reading this somewhere other than Build5Nines.com, it was republished without permission.)

 Microsoft Azure Regions: Interactive Map of Global Datacenters
Microsoft Azure Regions: Interactive Map of Global Datacenters
 Create Azure Architecture Diagrams with Microsoft Visio
Create Azure Architecture Diagrams with Microsoft Visio
 Stop Wasting Hours Writing Unit Tests: Use GitHub Copilot to Explode Code Coverage Fast
Stop Wasting Hours Writing Unit Tests: Use GitHub Copilot to Explode Code Coverage Fast
 IPv4 Address CIDR Range Reference and Calculator
IPv4 Address CIDR Range Reference and Calculator
 Byte Conversion Calculator from KB, MB, GB, TB, PB
Byte Conversion Calculator from KB, MB, GB, TB, PB




This is so new that I cannot find the “Bastion” resource to add to my subscription / vnet, nor can I find it within the Azure pricing documentation. Guess I will have to be a little more patient…
Any word on when this will be available in preview?
You can try it out by reading their step by step guide: https://docs.microsoft.com/en-us/azure/bastion/bastion-create-host-portal. I will try it out soon.
It’s now available under public preview
Yeah!!! same here. Can’t wait.
It’s under private preview. I’m guessing we’ll see more on this as we approach Ignite 2019.
Neither links to the videos are working now. Maybe they were released too early…
Neither links to the videos work anymore. Probably MS published them too early
They even removed the videos. Probably something that is not yet stable or limited to a small group of customers.
Maybe they were re-launching their content.
Here’s a link to their new announcement for it: https://azure.microsoft.com/en-us/services/azure-bastion/
Here’s a link to their docs: https://docs.microsoft.com/en-us/azure/bastion/bastion-create-host-portal
Yeah so it seems